As Mr Robot races to the conclusion of Season 3, Elliot is determined to stop the Dark Army from doing any more damage. The Dark Army, led by White Rose, has blown up 71 buildings. As you remember, Elliot’s system has been compromised and he wants to trace the malware back to its source and hack the Dark Army to gain control of their operations.

Elliot uses memory forensics tools to reverse engineer the Dark Army’s malware and send a malicious document to their command and control server to take over one of their clients. Like nearly everything in this fabulous TV show, the technical details are accurate and realistic. Elliot is seen using Volatility, the open source memory analysis tool to find the malware and his system and trace it back to its command and control server (for more on Volatility, see my article Digital Forensics, Part 2: Live Memory Acquisition and Analysis as well as our upcoming Digital Forensics online course) .

Then, Elliott crafted a malicious PDF (ecoin_vuln_notes.pdf) which gave him access to the Dark Army’s management interface. Once there, he was able to see everything – all the DA targets on a map.

In this tutorial, we will examine how Elliot was able to trace the Dark Army’s command and control server using Volatility.
Step #1: Finding the Key File
Volatilty is a Python script and is invoked in each of the following commands by using vol.py. Then, -f option is used to extract memory to a file Elliot names appropriately, out.mem. Then, each command must include a memory profile of the operating system (every operating system using RAM differently), in this case –profile=kali
In the first step, Elliot must find the key file. He enters the following command.
vol.py -f out.mem –profile=kali linux_find_file -f /etc/ld.so.preload

Here, Elliot is using the Volatility plugin, linux_find_file to search for the file (-f) /etc/ld.so.preload .
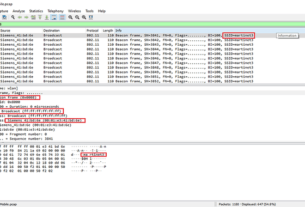
Volatility responds with the location (0xffff880028c740c0) of the file in memory as you can see near the bottom center.
Step #2: Elliot Sends the File in Memory to a New File
Next, Elliot enters the location of the file in memory that he found in the previous command and sends it to (-O) to a file called ld.so.preload.
vol.py out.mem –profile=kali linux_find_file -i 0xffff880028c740c0 -O ld.so.preload

Here, he is simply taking a file out of running, active memory and copying it to a new file so that he can examine it’s contents.
Step #3: Display the Contents of the File He Extracted from Memory
Here, Elliot simply displays the contents of this file that he extracted from memory using the cat command.
cat ldso.preload

The contents of the file are /usr/local/lib/libhd.so
Step #4: Find libhd.so in the Running Processes
In this step, Elliot is using another Volatility plugin, linux_proc_maps, to display all the processes running on his system and then piping (|) that to grep to filter for the process named libhd.so.
vol.py -f out.mem –profile=kali linux_proc_maps | grep libhd.so

As you can see, he found the process at PID 39238.
Step #5: Display the Process at PID 39238
That output displays that the process Elliot is looking for has PID (process ID) 39238. Elliot then uses that information to find PID 39238 and display it using the Volatilty plugin, linux_psaux.
vol.py -f out.mem –profile=kali =–pid=39328 linux_psaux

When Elliot runs this command, he can see the process at PID 39238. He can see that it is a Python script and it opens a URL at 192.251.68.228.
Elliot has found the URL of the Dark Army’s command and control server!
Now, he needs to send a document (ecoin_vuln_notes.pdf) with his rootkit to the command and control server to take control of their interface and short- circuit the Dark Army’s malicious plans.
This episode of Mr Robot is an excellent demonstration of the power of live memory forensics with Volatility and raises a legal and ethical issue of whether we can “Hack the Hacker“.
Keep coming back my hacker friends and fellow Mr. Robot fans as I attempt to demonstrate for you the Mr Robot Hacks!