Welcome back, my aspiring automobile cyber warriors!
Automobile hacking is the cutting edge of the hacking discipline!
Automobile and other vehicle hacking could have dramatic effects on society as we know it. Imagine a cyber war scenario where the opposing generals employ hackers to commandeer the adversaries tanks, jeeps and other vehicles. Or a bit more mundane, imagine a world where hackers can open, start and control your vehicle!
In previous tutorials, we have examined the basics of the CAN protocol, and then the can-utils, and the Metasploit interface to the CAN-based network.
In this tutorial we will set up a simulation environment where you can use some of this knowledge to analyze and hack a simulated vehicle.

This CAN Bus simulator was developed by Craig Smith at Open Garages and the author of The Car Hackers Handbook by No Starch Press.
Step #1: Install Dependencies
The first step is to install the necessary dependencies into your Kali system.
kali > apt-get install libsdl2-dev libsdl2-image-dev -y

Step #2: Install Can Utils
The next step is to install the CAN utils. These are a set of Linux-native utilities developed by Bosch of Germany. If you followed my second tutorial in the series, you have likely already installed these utilities. If not, you can do so now by downloading and installing them from the Kali repository.

Step #3: Download ICSim
Craig Smith, author of The Car Hackers Handbook and founder of opengarages.org has developed a small CAN simulator we will download and install next. You can clone it from github.com here.
kali > git clone https://github.com/zombieCraig/ICSim

Next, we navigate to the newly created directory, ICSim.
kali > cd ICSim

When we do a long listing on that directory, we can see numerous files. At this point, we need to execute the setup_vcan.sh script. This is a simple BASH script that loads the new kernel modules, can and vcan, using modprobe (for more on kernel modules, see Chapter 8 of Linux Basics for Hackers) and then creates a virtual CAN interface, vcan0.
Now, we need to execute this script .
kali > ./setup_vcan.sh

To start the instrument panel of our simulated vehicle, we simply need to execute icsim followed by the name of the virtual CAN interface, in this case, vcan0.
kali > ./icsim vcan0
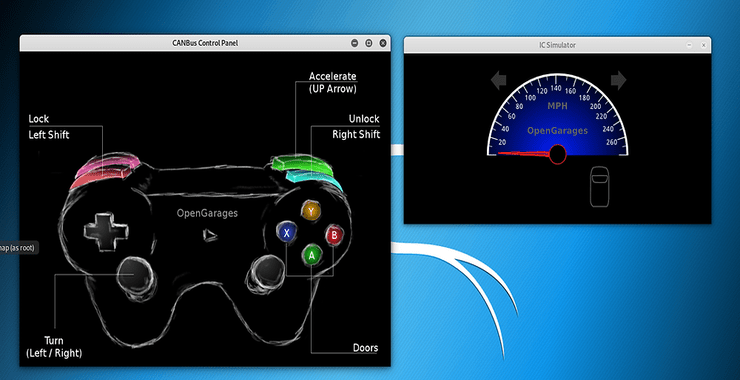
The instrument panel should appear on your desktop like below. It includes a speedometer, turn signal and a virtual vehicle silhouette similar to modern vehicles that indicate open and closed doors for the driver.

To start the controller of this vehicle, enter;
kali > ./controls vcan0

This should open the controller on your desktop as seen below.

If you have a game controller connected to your Kali system, you can now use it to “drive” your simulated car. If not, you can use the following keyboard combinations.

Now that we have our simulator setup and ready to go, in the next tutorials we will “drive” our simulated vehicle, sniff and observe the CAN bus messages and reverse engineer those CAN bus messages.
Summary
To study the CAN bus can be time consuming and expensive. Thankfully, Craig Smith has developed a simple CAN bus simulator where we can observe, study and reverse engineer CAN bus networks and signals. In the following tutorials we will do just that, so keep coming back my aspiring automobile cyber warriors!