In my first article in this Metasploit series, I introduced you to some of the key commands you need to know before using Metasploit. In this second article in the series, I want to introduce you the different types of modules found in Metasploit.

When you start Metasploit into the msfconsole, you are greeted by an opening splash screen similar to that below.

Notice near the bottom the screen that the interactive console opens with a msf > and slightly above there, Metasploit lists the number of modules by type. Metasploit has seven (7) type of modules. These are;
(1) exploits
(2) payloads
(3) auxiliary
(4) encoders
(5) post
(6) nops
(7) evasion (new in Metasploit 5)
We will examine each of these types of modules, so that we might better utilize them in our Metasploit pentesting/hacking.
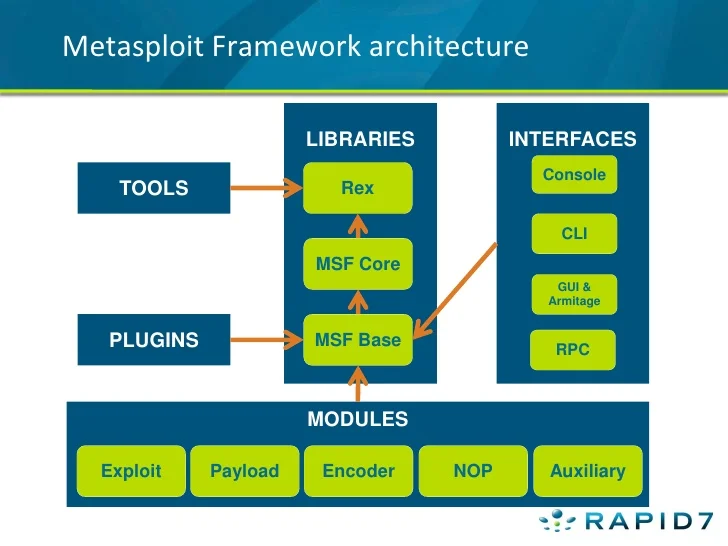
Metasploit Inner Architecture
The better you understand Metasploit, the more productive you will be with it. Although it is really unnecessary to understand the inner architecture of this powerful tool to get started, as you advance this knowledge will be become increasingly useful.
The diagram below visually depicts the architecture of Metasploit. For now, note the Interfaces to the right and the modules along the bottom
Metasploit Modules
Before entering the msfconsole, we can view the architecture of Metasploit from the command line in our BASH shell. Let’s go to Metasploit’s directory in Kali by typing;
kali > cd /usr/share/metasploit-framework
Then, do a long listing on that directory.
kali > ls -l
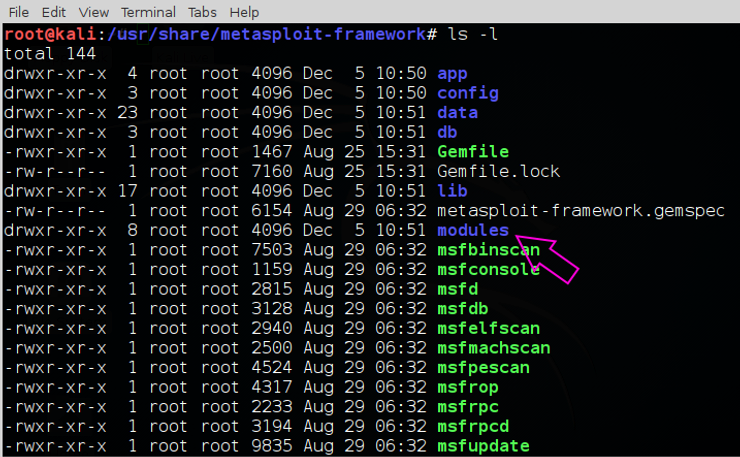
As you can see above, this directory has several sub-directories, but let’s concentrate on the modules directory for now. Navigate to it and do a long listing.
kali > cd modules
kali > ls -l
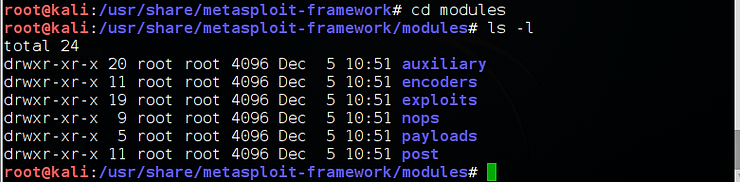
As you can see in the screenshot above, the modules directory contains the six sub-directories with each containing a separate type of module. We can open each of those directories to find each of the individual module types.
Exploits
Let’s begin with exploits as they essentially define this “exploitation” framework. These modules are code that was developed to take advantage or “exploit” a flaw or vulnerability in a system. We can view the exploits by navigating to the exploits directory and doing a long listing of its contents.
kali > cd exploits
kali > ls -l
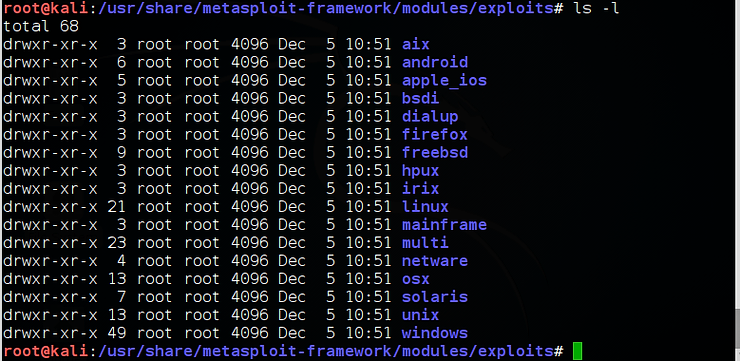
As you can see above, these exploits are sub-divided into sub-directories by the operating system they are designed to target.
Payloads
Next are “payloads“. These are what we leave behind on the exploited system that enables us to connect to or “own” the system. In other environments that might be referred to as listeners or in some cases, rootkits (rootkits are special type of payload. Not all payloads are rootkits).
Let’s navigate to that directory and list its contents.
kali > cd payloads
kali > ls -l
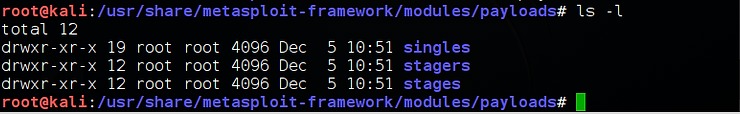
You can see above that the payloads are subdivided into three types;
(1) singles
(2) stagers
(3) stages
In my next tutorial in this series, I will detail the differences in each of these types of payloads, but for now, we can say that singles are small self-contained code designed to take some single action, stagers implement a communication channel that can be used to deliver another payload that can used to control the target system and finally, stages are larger payloads that provide control of the target such as the Meterpreter and VNC. We will provide more detail in the third installment of this Metasploit series.
Auxiliary
Auxiliary modules are modules that provide some other capability that does not easily fit into the other categories. These include such things as scanners, fuzzers, DoS, etc. modules. This is easily the fastest growing set of modules as Metasploit continues to expand into a full-scale exploitation framework that enables the hacker/pentester A-Z capability.
Let’s navigate to the auxiliary directory and do a long listing of its contents.
kali > cd auxiliary
kali > ls -l
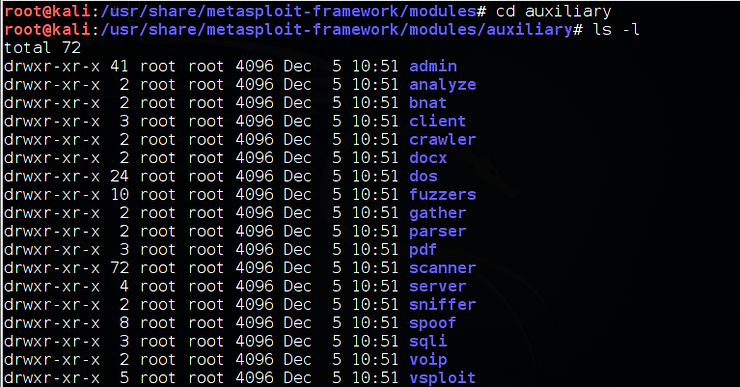
Here we can see that the auxiliary modules are subdivided by their purpose and target. Note the analyze, the scanner and the dos directories. These modules are used to analyze target systems, scan the target system and DoS the target systems, respectively.
Some of these modules are categorized by their target, such as the docx, pdf and voip directories.
Encoders
The encoder modules are designed to re-encode payloads and exploits to enable them to get past security defense systems such AV and IDS’s.
Let’s navigate to that directory and view its contents with a long listing.
kali > cd encoders
kali > ls -l
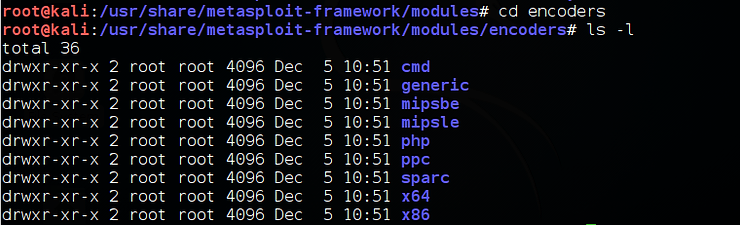
The encoders are subdivided by type of CPU such as x64, x86, sparc, ppc and mips and also by type of code such a cmd and php. Obviously, we need to use the appropriate encoder based upon the target system.
Post
Post is short for post-exploitation. These are modules that are used after exploitation of a system. These modules are often used after the system has been “owned” and has the Meterpreter running on the system. These can include such modules as keyloggers, privilege escalation, enabling the web cam or microphone, etc. See Part 15 of this series for more on post-exploitaion.
Let’s navigate to the post directory and do a long listing of its contents.
kali > cd post
kali > ls -l
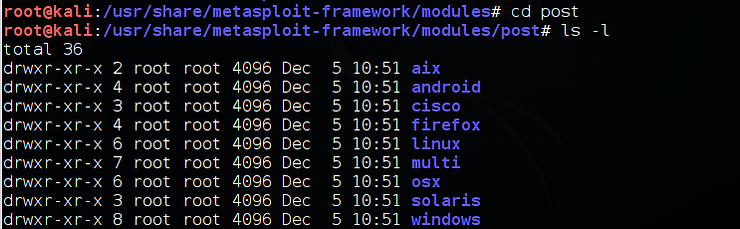
As you can see these modules are subdivided by target OS.
NOPS
In machine language, a NOP is short for “no operation”. This causes the system’s CPU to do nothing for a clock cycle. Often, NOP’s are essential for getting a system to run remote code after a buffer overflow exploit. These are often referred to as “NOP sleds”. These modules are used primarily to create NOP sleds.
Let’s navigate to the nops directory and do a long listing of its contents.
kali > cd nops
kali > ls -l
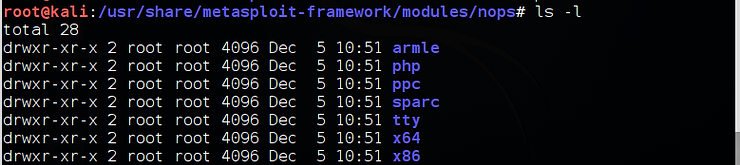
We can see above that they are subdivided by target OS.
If you want to become a Metasploit expert, sign up for my upcoming Metasploit Kung-Fu course here.