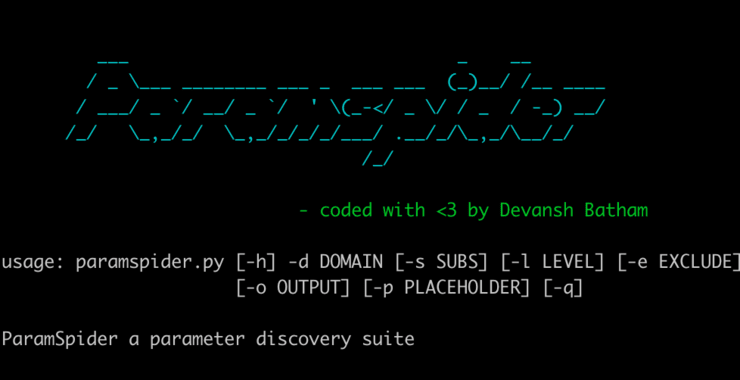
The Cyber Cossacks: Hackers-Arise’s New School in Kharkiv, Ukraine!
Ukrainian officials have requested that Hackers-Arise open a new cybersecurity/hacker school in Ukraine to train the next generation of cyber cossacks to protect Ukraine. These classes will begin in January 30, 2023 and is open to talented and motivated Ukraine citizens who are interested in protecting Ukraine from further Russian cyber attacks. Kharkiv is […]
Continue Reading