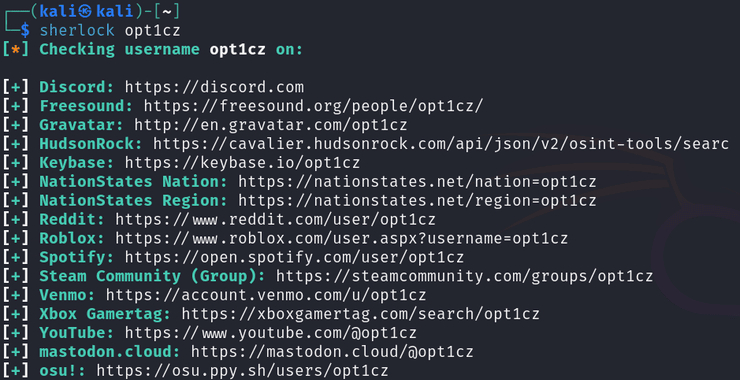
Open-Source Intelligence(OSINT): Sherlock – The Ultimate Username Enumeration Tool
Welcome back, aspiring OSINT investigators! Social media platforms hold a wealth of personal and professional information, making them valuable for reconnaissance in penetration testing and cyberwarfare operations. Sherlock is a lightweight yet powerful tool designed to search for social media profiles using a username. In this article, we’ll guide you through installing and using […]
Continue Reading